Hi all,
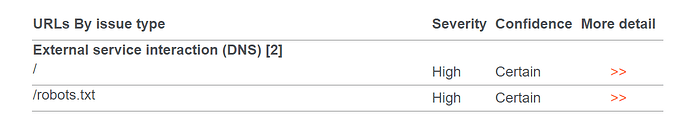
We just did a security scan on the geonetwork 3.10.6 (using Burp Collaborator). And we received two high vulnerabilities about the DNS lookup. I wonder if anyone can provide some insights on how to resolve this, or if this is an intended behavior. Thank you.
External service interaction (DNS)/### Issue detail:It is possible to induce the application to perform server-side DNS lookups of arbitrary domain names.
The payload https://hm7zarxlruwd1dwkcihycewz2q8jwak38yvpje.burpcollaborator.net/ was submitted in the Referer HTTP header.
The application performed a DNS lookup of the specified domain.
Issue background
External service interaction arises when it is possible to induce an application to interact with an arbitrary external service, such as a web or mail server. The ability to trigger arbitrary external service interactions does not constitute a vulnerability in its own right, and in some cases might even be the intended behavior of the application. However, in many cases, it can indicate a vulnerability with serious consequences.
In cases where DNS-based interactions can be triggered, it is normally possible to trigger interactions using other service types, and these are reported as separate issues. If a payload that specifies a particular service type (e.g. a URL) triggers only a DNS-based interaction, then this strongly indicates that the application attempted to connect using that other service, but was prevented from doing so by egress filters in place at the network layer. The ability to send requests to other systems can allow the vulnerable server to be used as an attack proxy. By submitting suitable payloads, an attacker can cause the application server to attack other systems that it can interact with. This may include public third-party systems, internal systems within the same organization, or services available on the local loopback adapter of the application server itself. Depending on the network architecture, this may expose highly vulnerable internal services that are not otherwise accessible to external attackers.
Issue remediation
You should review the purpose and intended use of the relevant application functionality, and determine whether the ability to trigger arbitrary external service interactions is intended behavior. If so, you should be aware of the types of attacks that can be performed via this behavior and take appropriate measures. These measures might include blocking network access from the application server to other internal systems, and hardening the application server itself to remove any services available on the local loopback adapter.
If the ability to trigger arbitrary external service interactions is not intended behavior, then you should implement a whitelist of permitted services and hosts, and block any interactions that do not appear on this whitelist.
References
Vulnerability classifications
- CWE-918: Server-Side Request Forgery (SSRF)
- CWE-406: Insufficient Control of Network Message Volume (Network Amplification)
Request:GET / HTTP/1.1 Host: ***** Upgrade-Insecure-Requests: 1 Accept-Encoding: gzip, deflate Accept: / Accept-Language: en-US,en-GB;q=0.9,en;q=0.8 User-Agent: Mozilla/5.0 (Windows NT 10.0; Win64; x64) AppleWebKit/537.36 (KHTML, like Gecko) Chrome/89.0.4389.128 Safari/537.36 Connection: close Cache-Control: max-age=0 Referer: https://hm7zarxlruwd1dwkcihycewz2q8jwak38yvpje.burpcollaborator.net/
Response:HTTP/1.1 200 Server: nginx/1.19.8 Date: Wed, 14 Apr 2021 18:09:59 GMT Content-Type: text/html;charset=UTF-8 Connection: close Set-Cookie: serverTime=1618423798246; Path=/ Set-Cookie: sessionExpiry=1618423798246; Path=/ Pragma: no-cache Cache-Control: no-cache Expires: -1 Access-Control-Allow-Credentials: true Access-Control-Allow-Methods: GET, POST, OPTIONS Access-Control-Allow-Headers: Accept,Accept-Encoding,DNT,X-Mx-ReqToken,Keep-Alive,User-Agent,X-Requested-With,If-None-Match,If-Modified-Since,Cache-Control,Content-Type,Pragma,Origin,Referer Strict-Transport-Security: max-age=63072000; includeSubDomains; preload Content-Length: 17987 <script async=“async” type="text/javascri
Snip
Collaborator DNS interaction:
The Collaborator server received a DNS lookup of type AAAA for the domain name hm7zarxlruwd1dwkcihycewz2q8jwak38yvpje.burpcollaborator.net.
The lookup was received from IP address 12.227.230.11 at 2021-Apr-14 18:09:58 UTC.
···
Zhuoyue Zhou