Hi there,
Have recently been twiddling with LDAP Role Service on GeoServer and seem to be coming across a problem where a local user from the defaut XML role store will work, but an LDAP user won’t
This seems to have happened in the past but appears to have been resolved: [GEOS-7327] Access to REST endpoints blocked when using LDAP authentication - JIRA
PS C:\Users\usr> curl --basic -v -u <LDAP username> -XGET http://dev-geoserver.gdnnet.lan/geoserver/rest/workspaces.xml
[ ..]
HTTP Status 403 – Forbidden
The server understood the request but refuses to authorize it.
Apache Tomcat/9.0.107
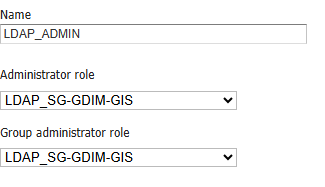
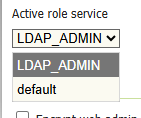
Lookup to the roles appears to be handled correctly, have added the LDAP role into rest.properties and this then appears in the log trace. I am a member of LDAP_SG-GDIM-GIS and this is also declared as admin
08 Dec 18:16:33 DEBUG [geoserver.security] - Converted URL to lowercase, from: '/rest/workspaces.xml'; to: '/rest/workspaces.xml' and httpMethod= GET
08 Dec 18:16:33 DEBUG [geoserver.security] - ~~~~~~~~~~ antPath= /** methodList= [GET]
08 Dec 18:16:33 DEBUG [geoserver.security] - Candidate is: '/rest/workspaces.xml'; antPath is /**; matchedPath=true; matchedMethods=true
08 Dec 18:16:33 DEBUG [geoserver.security] - returning ADMIN,LDAP_SG-GDIM-GIS
Running the same command as a local user in the ADMIN group returns OK!
PS C:\Users\usr> curl --basic -v -u sa_geoserver_inspire -XGET http://dev-geoserver.gdnnet.lan/geoserver/rest/workspaces.xml
[...]
<workspaces>
[....]
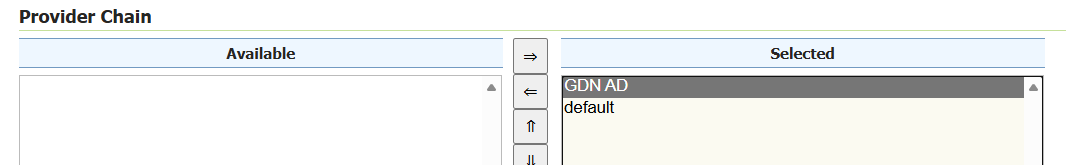
Swapping the provider chain around so that the LDAP user is above default doesn’t deliver a good result. Hierarchical group search on/off doesn’t seem to impact either. Have tried using the user@domain and DOMAIN\user syntax for logging in, still get a 401.
It feels like the REST API just isn’t consulting the LDAP Role Service?
Would be really grateful or any input.
Joey